@Ledger crypto wallet presented an "exciting update": a recovery function for the hardware wallet's seed phrase. So why do people seem to be not excited about that?
Exciting update, Ledger has a new product, Ledger Recover, that’s launching soon: https://t.co/nT1VHnnSYz
— Ledger (@Ledger) May 16, 2023
🧵Here’s what Ledger Recover is and what it isn’t, explained by @P3b7_ & in the thread below. pic.twitter.com/RW1w07H6pK
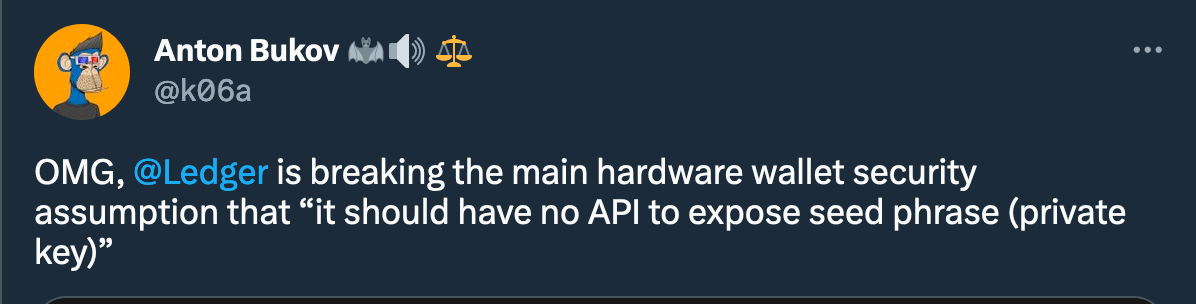
Simply put, it's all about an ID-based recovery service for users' seed phrases. To use it, one must provide a passport or national identity card for identity confirmation. The service works by distributing encrypted fragments to three third-party custodians.
So… just connect your crypto seed phrase with your passport (what a rare cryptographic feel!), and don't worry: every custodian only gets a fragment of your seed!
"Each fragment is useless on its own and can only be decrypted on a Ledger. They are completely safe," – a Ledger spokesperson told Decrypt.
But…
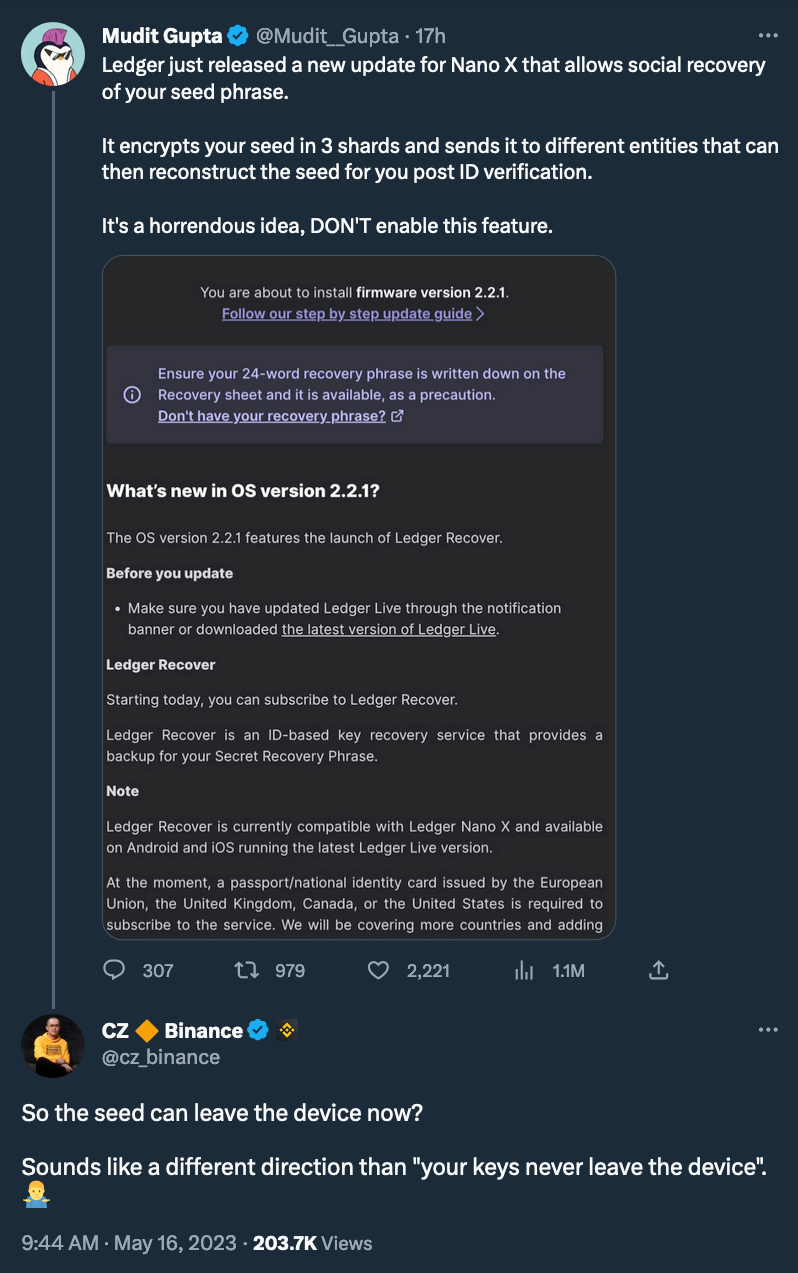
The most spiteful critics also remind us about users' data breach from a Ledger back in 2020, which exposed personal information, such as phone numbers, physical addresses of approximately 300,000 customers, and over 1 million email addresses.
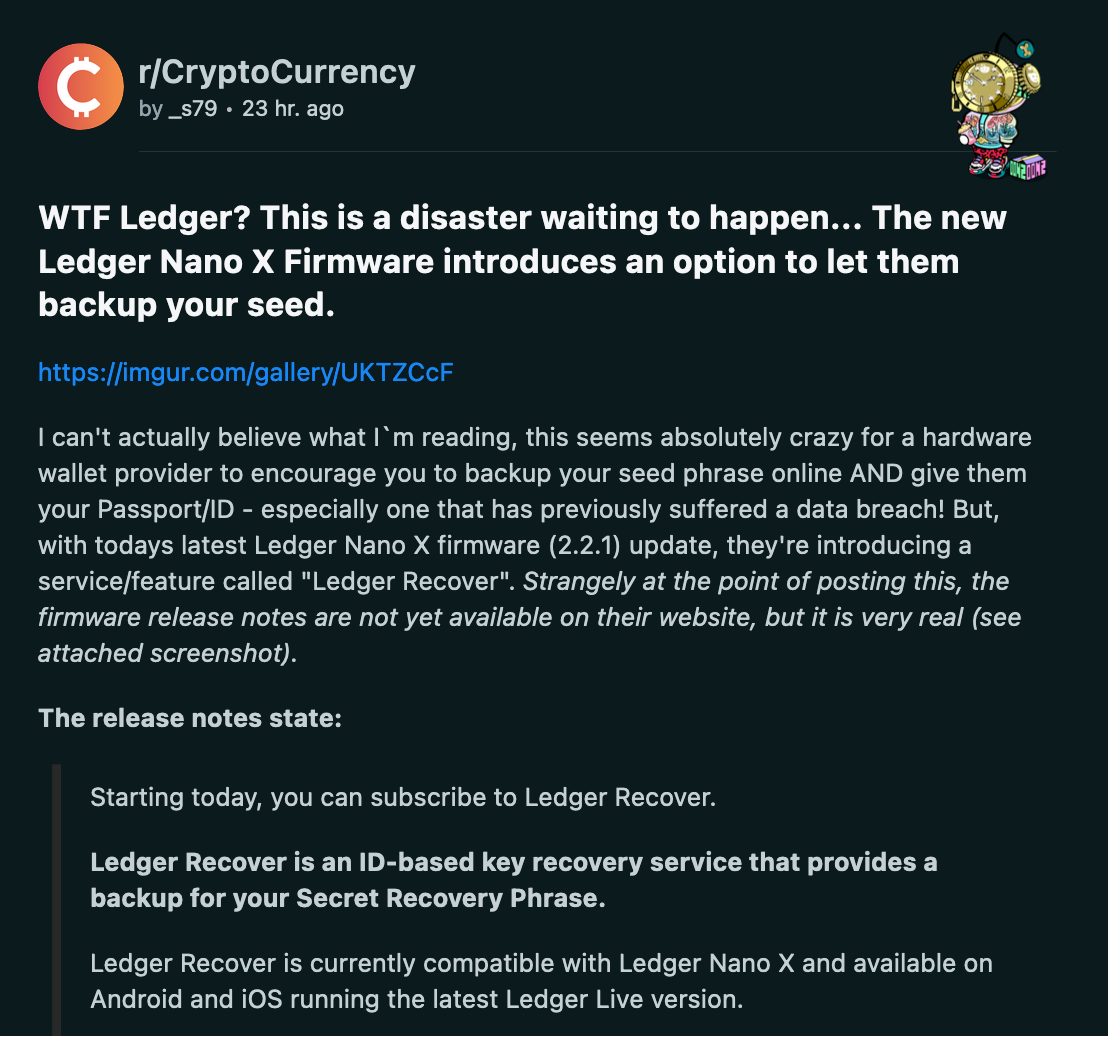
As Decrypt points out, if the same data leak happened to Ledger Recover users, the hacker could possibly use the service to "recover" the seed phrase.
Meanwhile, Ledger asserts that providing a government ID alone does not pose a security risk as it is just one step in the process. Ledger representatives explain that the company employs advanced liveness detection that includes randomized prompts using a camera to prevent the process from being faked or pre-recorded. Before the recovery process begins, both technology and human review are conducted to ensure a match, so even if someone steals your government ID, they cannot retrieve your Secret Recovery Phrase (SRP).
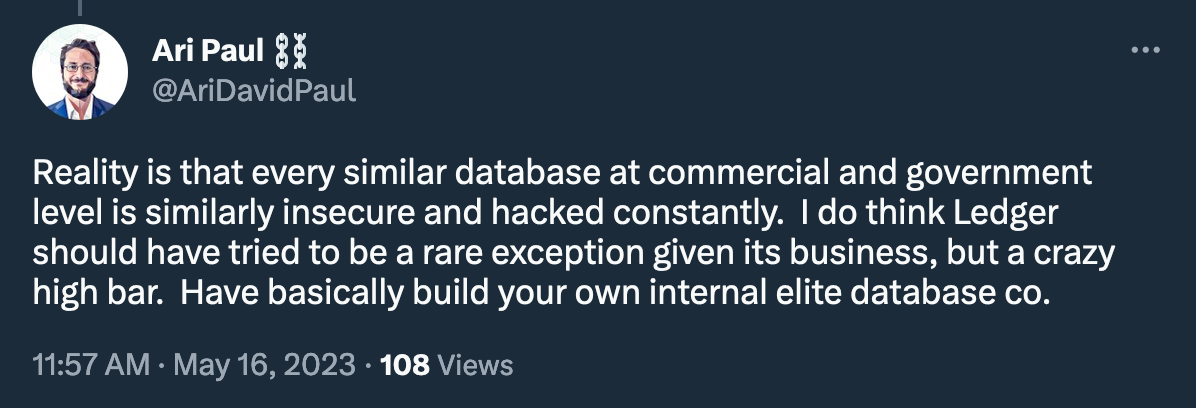
But the frequency with which user data leaks from all sorts of centralized services cannot but raise concerns about creating such a centralized point of failure. After all, social engineering techniques have been one of the most effective ways to steal data, even from quite advanced vaults.
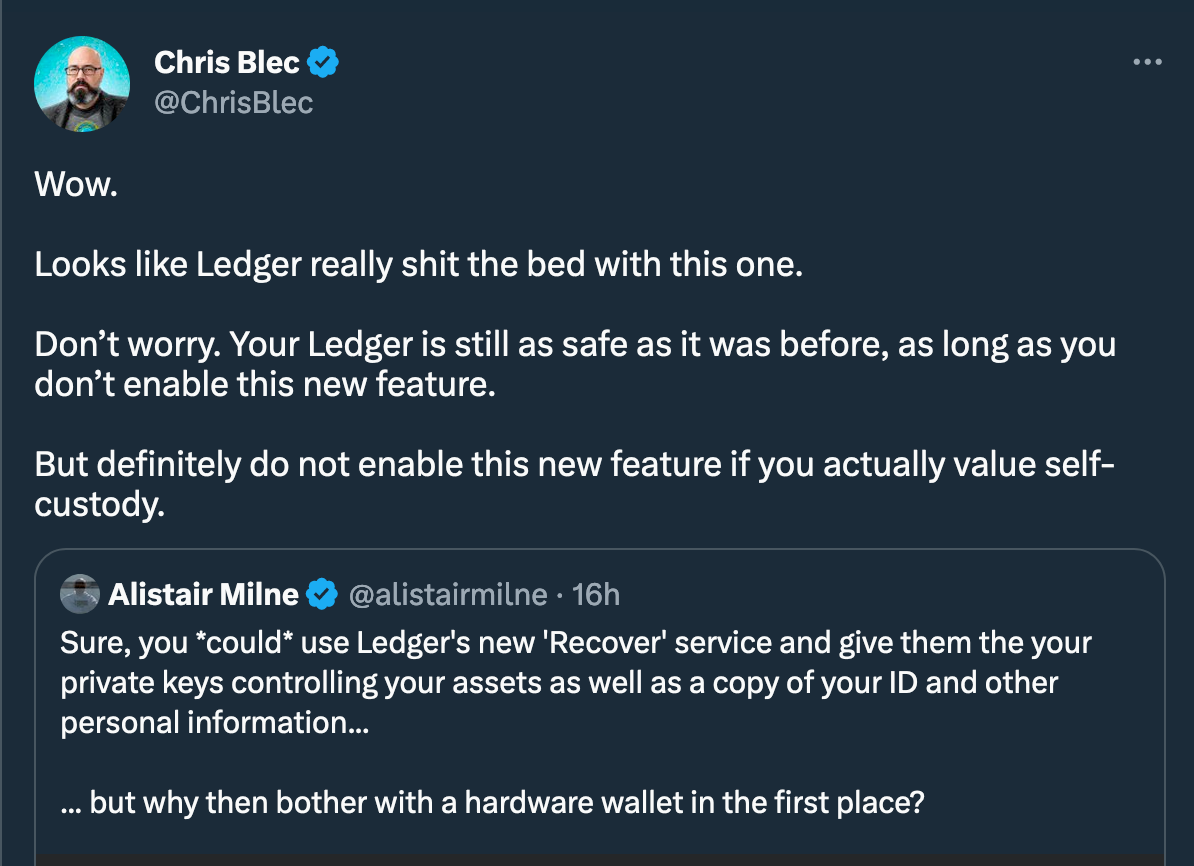
And indeed, citing Alistair Milne,
"Sure, you *could* use Ledger's new 'Recover' service and give them your private keys controlling your assets as well as a copy of your ID and other personal information… but why then bother with a hardware wallet in the first place?"